Contact Michael Cena
Email & Phone Number
VP & Head of Cyber Security at A+E Networks
Michael Cena Email Addresses
Michael Cena Phone Numbers
Michael Cena's Work Experience






Mizuho Corporate Bank, Ltd
Sr. Security Engineer
September 2006 to December 2007




Vice President, Head of Cyber Security
Show more
Show less
Michael Cena's Education
MIT Sloan School of Management
January 2019 to January 2021
MIT Sloan School of Management
January 2019 to January 2020
Stanford University Graduate School of Business
Marine Corps Communications and Electronics School
Show more
Show less
Frequently Asked Questions about Michael Cena
What is Michael Cena email address?
Email Michael Cena at [email protected] and [email protected]. This email is the most updated Michael Cena's email found in 2024.
What is Michael Cena phone number?
Michael Cena phone number is +1.5408458834.
How to contact Michael Cena?
To contact Michael Cena send an email to [email protected] or [email protected]. If you want to call Michael Cena try calling on +1.5408458834.
What company does Michael Cena work for?
Michael Cena works for A+E Networks
What is Michael Cena's role at A+E Networks?
Michael Cena is Senior Director, Head of Cyber Security
What industry does Michael Cena work in?
Michael Cena works in the Information Technology & Services industry.
Michael Cena's Professional Skills Radar Chart
Based on our findings, Michael Cena is ...
What's on Michael Cena's mind?
Based on our findings, Michael Cena is ...
Michael Cena's Estimated Salary Range
Michael Cena Email Addresses
Michael Cena Phone Numbers
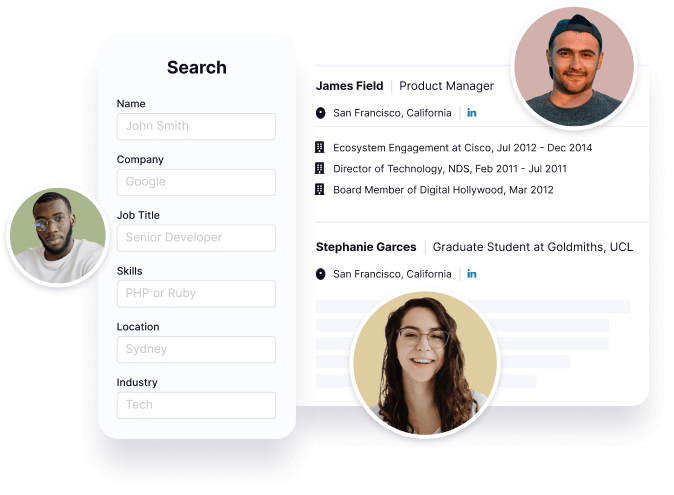
Find emails and phone numbers for 300M professionals.
Search by name, job titles, seniority, skills, location, company name, industry, company size, revenue, and other 20+ data points to reach the right people you need. Get triple-verified contact details in one-click.In a nutshell
Michael Cena's Personality Type
Introversion (I), Sensing (S), Thinking (T), Perceiving (P)
Average Tenure
2 year(s), 0 month(s)
Michael Cena's Willingness to Change Jobs
Unlikely
Likely
Open to opportunity?
There's 94% chance that Michael Cena is seeking for new opportunities





























Michael Cena's Social Media Links
/in/mikecena /company/aenetworks /redir/redirect /school/mit-sloan-school-of-management/